I recently had a déjà vu experience. About a year ago, I wrote about a fraudulent email I received while preparing to deliver a virtual workshop on P-Card risk analyses. This prompted me to share tips and statistics related to information security, and recommend Verizon’s Data Breach Investigations Report as a resource. The same things are occurring again. Another fraudulent email landed in my inbox (different topic this time), another virtual workshop on risk analyses is coming up, Verizon released a new report, and this post offers additional security tips. Keep reading to learn more and see images of the fraudulent emails.
Phishing
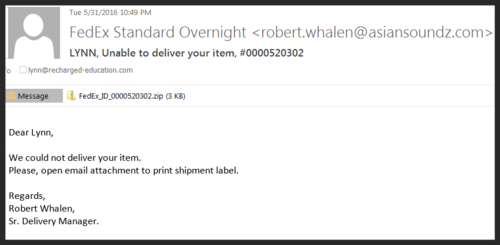
There is no shortage of social engineering tactics. Among the most common are phishing expeditions designed to entice people to click links or email attachments that open the door to fraudsters and their malicious software. Last year, I received a fake FedEx email. This month, it was a fake Dropbox email with a link to view an invoice. Ensure your AP department is aware of this scam. While it is not new, they might not have encountered it previously. See related images in the adjacent column.
Per Verizon’s 2017 Data Breach Investigations Report:
- 7.3% of users across multiple data contributors were successfully phished—whether via a link or an opened attachment.
In a typical company (with 30 or more employees), about 15% of all unique users who fell victim once, also took the bait a second time.
While 7.3% is not huge, just one successful phishing incident can have far-reaching consequences.
Training Tips
In my related blog post last year (“Attack fraud through training”), I noted that cardholders should be able to differentiate between legitimate communications from the card issuer and fraudulent ones.
To enhance your training efforts, can your issuer share examples of fraudulent emails that target cardholders, as well as real ones that they send? Also train cardholders to pause and evaluate any emails appearing to be from the issuer. For example:
- Were they expecting an email (e.g., you told them something would be sent pertaining to “X” topic) or is the communication a surprise, which might indicate potential fraud?
- Is the sender’s email address consistent with your issuer’s email addresses? Per the images in the next column, fake emails typically reflect odd addresses.
- Does the email stress urgency (e.g., “You must click here ASAP!”) or include a threat (e.g., “Failure to complete this action could result in card deactivation.”)?
If your training includes a quiz element, then add something related to phishing, such as: If you receive an email that appears to be from the bank and it directs you to click a link to update your contact information, what is the BEST action to take?
Besides NOT clicking on anything, cardholders should notify the appropriate internal party. You/your organization needs to stay informed and take any necessary action (e.g., alerting other cardholders, contacting your issuer, etc.).
Finally, if possible, as part of a process audit, simulate a phishing email to test cardholders’ reactions Do they click on anything? Do they report the suspicious email?
Fraudulent Email Images
Below are the emails mentioned earlier. In each, the sender’s email address has nothing to do with FedEx or Dropbox.
Virtual Workshop
P-Card Risk Analysis
Information security is just one of many topics that I will cover in the three-hour June 21 workshop hosted by AP Now. If you have not completed a robust P-Card program risk analysis recently, this workshop is for you. Registrants will also receive two bonus items:
- P-Card risk analysis template with more than 100 questions to help you assess your controls
- Guide on revitalizing your P-Card policies and procedures.
Please visit the AP Now website to learn more and register.
About the Author
Blog post author Lynn Larson, CPCP, is the founder of Recharged Education. With more than 15 years of Commercial Card experience, her mission is to make industry education readily accessible to all. Learn more…
Subscribe to the Blog
Receive notice of new blog posts.